Looking to connect with verified exhibitors and attendees at InCyber Forum Europe 2026, held in Lille, France? As one of Europe’s leading cybersecurity and digital trust events, InCyber Forum brings together global cyber leaders, government representatives, technology innovators, security strategists, and enterprise decision-makers.
Whether you’re launching advanced cybersecurity solutions, building strategic alliances, promoting digital trust services, or targeting CISOs and IT directors, our InCyber Forum Europe 2026 contact database gives you direct access to verified professionals driving innovation in cyber defense, data protection, and digital transformation.

Connect with verified cybersecurity and digital security decision-makers at InCyber Forum Europe 2026, segmented for precise B2B outreach.
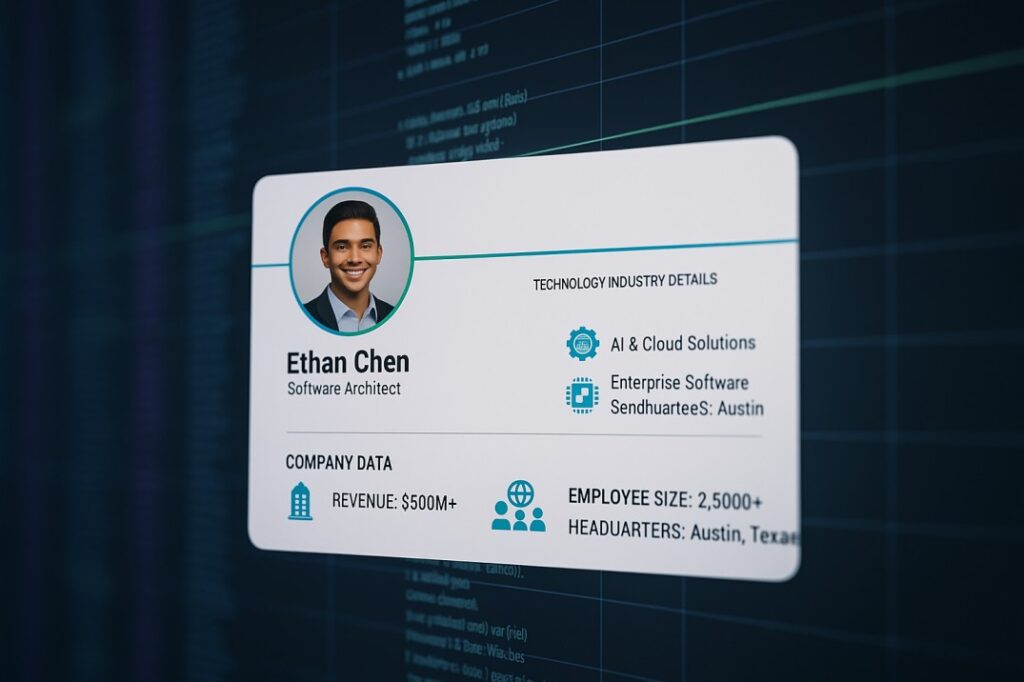
Included Data Points:
Use our InCyber Forum Europe contacts to schedule high-value meetings, generate qualified leads, strengthen partnerships, and expand your footprint in the European and global cybersecurity markets.


Get your preview sample of the InCyber Forum Europe 2026 Exhibitors List with verified emails and connect directly with cybersecurity innovators, IT security experts, compliance leaders, and enterprise decision-makers.
Powered by ExpoCaptive, this exclusive dataset ensures accurate, real-time outreach—helping you book more meetings, secure strategic partnerships, and grow your business in the rapidly evolving cybersecurity ecosystem.
👉 Experience the quality of our verified InCyber Forum Europe 2026 contacts with a complimentary sample before you commit!
Precision Audience Targeting – Engage CISOs, CIOs, IT Security Directors, Risk & Compliance Heads, Data Protection Officers, cyber strategists, and government cyber officials seeking advanced security solutions and partnerships.
Multi-Channel Outreach – Leverage the database for LinkedIn campaigns, direct email marketing, ABM strategies, and pre- or post-event engagement to convert connections into long-term opportunities.
Rich Contact Profiles – Each profile includes company insights, verified decision-maker titles, specialization details, and validated contact information to support personalized B2B campaigns and enterprise sales.
Industry-Aligned Segmentation – Segment contacts by business type, cybersecurity focus, company size, revenue, region, or technology specialization for accurate, solution-driven targeting.
Get access to both upcoming and past event editions, complete with verified post-event attendees and exhibitor lists. Every list is thoughtfully curated with accurate contact details of decision-makers, industry experts, and exhibiting companies—helping you build the right connections and maximize your outreach.
Step 1: Data Sourcing & Collection
We gather relevant data from a wide range of sources, including global subscriptions, trade shows, directories, e-books, news agencies, and more. This ensures we capture a diverse set of contacts to meet specific business needs.
Step 3: Data Validation & Authenticity Check
Each record is validated against our master database and cross-verified with social media platforms to confirm authenticity. A manual inspection ensures the highest level of accuracy for every contact.
Step 5: Consent & Compliance Assurance
We run AB-tested opt-in email campaigns and tele-verification checks to ensure consent and compliance with global data protection regulations like GDPR and CAN-SPAM. Only verified, legitimate data is finalized and ready for outreach.
Step 4: Data Cleaning & Quality Assurance
Using statistical techniques, we clean and refine the data, identifying and correcting anomalies. A rigorous manual inspection further ensures that the data is high-quality, reliable, and ready for use.
Step 1: Data Sourcing & Collection
We gather relevant data from a wide range of sources, including global subscriptions, trade shows, directories, e-books, news agencies, and more. This ensures we capture a diverse set of contacts to meet specific business needs.
Step 2: Data Enrichment & Segmentation
Missing fields are appended to incomplete records using advanced machine learning tools. This process helps us build a comprehensive and segmented contact list, ensuring data relevance and precision.
Step 3: Data Validation & Authenticity Check
Each record is validated against our master database and cross-verified with social media platforms to confirm authenticity. A manual inspection ensures the highest level of accuracy for every contact.
Step 4: Data Cleaning & Quality Assurance
Using statistical techniques, we clean and refine the data, identifying and correcting anomalies. A rigorous manual inspection further ensures that the data is high-quality, reliable, and ready for use.
Step 5: Consent & Compliance Assurance
We run AB-tested opt-in email campaigns and tele-verification checks to ensure consent and compliance with global data protection regulations like GDPR and CAN-SPAM. Only verified, legitimate data is finalized and ready for outreach.






Here is what our clients are saying about their success with us, in their own words.


ExpoCaptive’s accurate event mailing lists saved us hours and delivered high-quality, personalized leads quickly. They truly understand our business needs.
Sarah Mitchell
Business Development Manager


ExpoCaptive helped us find niche trade show buyers, opening new doors. In just 3 months, our ROI grew 20%. Highly recommended for event marketing success.
Michael Anderson
Marketing Director


Managing multiple events was tough. ExpoCaptive’s curated databases made reaching the right attendees easy, saving our team time and boosting event attendance.
Emily Thompson
Sales Head


ExpoCaptive helped us focus on events that truly matter, letting us target the right audience and use our resources efficiently, transforming our strategy.
David Miller
CEO
Boost business development, networking, and revenue growth with our curated Exhibitors and Attendees Lists for InCyber Forum Europe 2026. Connect directly with cybersecurity executives, IT security experts, government officials, and digital transformation leaders shaping the future of cyber resilience.
Order your list today and unlock powerful business opportunities in cybersecurity, AI security, cloud protection, digital identity, and critical infrastructure defense.